[img_reflect_center src=”https://hockadayfourcast.org/wp-content/uploads/2013/09/main-use.jpg”]
[dropcap]Brazilian President Dilma Rousseff postponed her scheduled October meeting with U.S. President Barack Obama on Sept. 17, bluntly citing her reasons in a statement released by her office: a “lack of…explanations and commitment to cease interceptive activities.”[/dropcap]
None other than computer specialist Edward Snowden is the source of these disclosures that U.S. intelligence spied on Brazilian political and business leaders. And this instance is only one of the various diplomatic fallouts the Obama administration has had to handle due to issues with privacy.
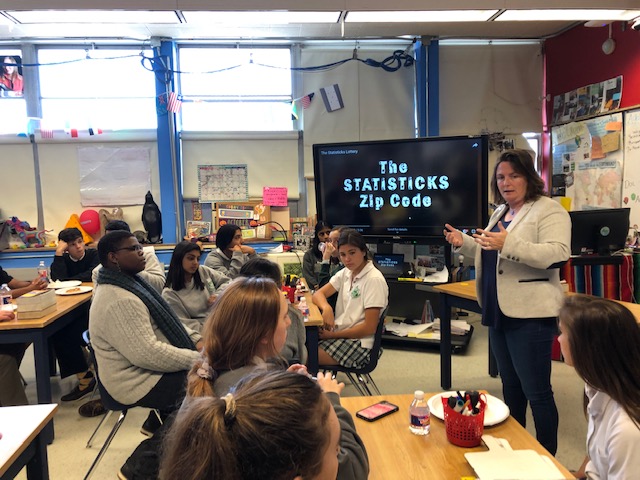
These clandestine activities first leaked by British newspaper The Guardian in May shocked many around the world like Rousseff. But back in Dallas, at a laptop school like Hockaday, it should come as no surprise that some administrators can always gain access to students’ personal accounts. Now these administrators are telling all—how they track students in a laptop school, the repercussions of their actions on digital platforms and the significance of making wise choices online.
At Hockaday
With all Hockaday laptops sharing a network, there are multiple tracking software the Technology Department has installed on each laptop. “We want to be as transparent as possible,” Technology Department Chair Jason Curtis said.
DyKnow, an instructional tool with which teachers can view students’ screens and restrict their use of certain programs upon will, is the most well-known one. Teachers can essentially look at students’ desktops without their knowing.
Administrators can also turn on students’ computer cameras at will. The school could do so through CompuTrace, a tool that allows organizations to remotely track computers. However, in order to do so, the school must file a police report because the school uses CompuTrace solely for laptop recovery. “It can help if a laptop has been stolen to possibly see where it is,” Curtis said.
CompuTrace does not function while students are at home, an ability that some Hockaday students fear is possible on their laptops. In 2010, Harriton High School in Rosemont, Pa. faced a lawsuit in possible violation of the law when it activated web cameras on students’ school-owned laptops when the students were home. However, Curtis said, at Hockaday, “everything we do can only happen here.” The Technology Department actually has no access to the program—only administrators at CompuTrace can remotely activate webcams.
Curtis said the school is moving away from the program, and it is not present in the new Lenovo ThinkPad PCs the school introduced this year, although the program is still installed on the old Toshiba laptops and last year’s Lenovo ThinkPads. “We didn’t see a lot of gains,” he said.
Another rumor is that the school has a filter for profanity on Outlook email. Curtis clarified that there is a filter on Outlook but only for external communication coming in—not internal communication. The absence of a filter for internal communication reflects a trust that students will behave appropriately online. “We have certain expectations for how you behave in person, and that’s what we expect online,” Curtis said.
There is no filter for student files. Even if someone possessed alarming documents on their laptop, the school would not know unless a concern was brought forth. Curtis said no one at Hockaday has brought a concern to him where he had to investigate a student’s files.
Hockadaisies also often complain about certain websites “blocked” on the Hockaday network. The school has implemented an Internet filter: Barracuda Web Filter, which has a broad list of categories: bandwidth, commerce, communications, information, leisure, liability, propriety, security, technology and safe browsing. Each category has different subcategories, and Curtis can choose to block or unblock certain subcategories. Persons using the Hockaday network actually have access to more sites than do those using the Guest Network.
One question plagues Curtis: how much freedom to give older students online while still protecting younger children from potentially harmful sites.
The Children’s Internet Protection Act offers him some guidance. Enacted by Congress in 2000, it sets guidelines for schools and libraries concerning a minor’s access to certain obscene or harmful content on the Internet. Some of the guidelines include limitations on pornography or unauthorized access.
Curtis wants students to know that the software and filters in place at Hockaday are not there to spy on students. “What we do is to enhance the instructional process,” he said.
Technology Board Chair senior Jennifer Kwon agreed. Referring to the blocking of certain social networking websites like Facebook during school hours, she said, “It’s so easy to get distracted taking notes during class, and it’s just not respectful to the teacher when she’s lecturing you. That’s what we consider when deciding which sites to block.”
Consequences
The repercussions for what students do online are real.
Any concern brought forth usually goes to Dean of Student Life Meshea Matthews to investigate. “I have a lot of conversation with those involved,” she said. Should she think a violation has occurred, she speaks with Upper School Head John Ashton and, afterwards, the Disciplinary Committee to consider the appropriate actions to be taken.
The Disciplinary Committee consists of Matthews, Ashton and two faculty members—Upper School English teacher Janet Bilhartz and Upper School Latin teacher Dr. Andre Stipanovic, who have each served seven years on the committee.
Consequences can include suspensions, days of separation from students, written reflection pieces or grade penalties, but Matthews said expulsion usually requires a prior violation.
Although different from laptops, cellular devices are still a widespread digital platform for students. Most do not know that the school does have the right to know the content of a student’s phone should a concern be brought forward. However, Matthews emphasized that an occurrence like this “only happens once in a blue moon.” Because of the disciplinary process’s confidentiality, she declined to release names of students who have experienced the process.
“It’s easy to just take a picture because you think it’s funny, but it’s serious,” Matthews said. An explicit image sent via text, email or any digital platform can have serious consequences: there are federal laws on child pornography. According to the U.S. Code section Title 18, Chapter 110, Section 225A (6), any person who “knowingly receives, or distributes, any visual depiction…by any means including by computer, or knowingly reproduces any visual depiction for distribution using any means” can be charged of child pornography.
This renders minors also potentially culpable of such an offense.
Honor Council Chair senior Christine Smith said the most common offense at Hockaday on digital platforms is misrepresentation online, possibly by sending an email pretending to be someone else or by claiming to turn in an assignment online on time when the student did not.
But with more and more assignments turned in online via Turnitin or Haiku Learning, it is becoming increasingly difficult for students to counterfeit the times their assignments were turned in. “Especially when students know they’re turning a paper into something like Turnitin, [the site] tells them right there if they’ve plagiarized,” Smith said.
But a larger problem in the digital world might exist: cyber-bullying. “I suspect there are more students who abuse social media to harass and bully,” Matthews said.
Hockaday’s Acceptable Use Policy clarifies that there will be consequences for any student discovered threatening, harassing or bullying others. Matthews said the school does not want to police the Internet, but it stands by the law. “We don’t have the mindset to catch girls,” she said. “We’re here to support the students.”
The school does not actively track students on social media platforms, nor do teachers create false accounts and “friend” or “follow” students to investigate them. Matthews said that teachers are not interested in examining their students’ lives on digital platforms. But she urged students to take a pause before posting or sending something. “They should consider their electronic etiquette,” she said. This etiquette could apply not just among students but also between students and teachers.
A teacher might receive a seemingly aggressive email from a student and forward that email to Matthews, who would then invite the student to have a conversation with her to understand the way the email was received. “I ask her to read the email aloud,” she said, cautioning students to examine their choice of tone.
She wants students to understand the idea of permanence—anything online is “captured forever,” Matthews said. “How difficult will it be to explain something later? Anything that gives a cause for doubt will be difficult to go away.”
Actions online could affect future applications for jobs, student government positions and even universities, even though Director of College Counseling Carol Wasden said universities do not typically check student social media accounts during the process. “The reality is, during the application process, it doesn’t happen,” Wasden said. “They’re uninterested and don’t have the time.”
But colleges do check periodically. “It’s highly unpredictable. You never know,” she said. However, once decisions are released, colleges do monitor comments on social media platforms about their universities. This means that institutions can revoke their decisions should they see an offensive post. “There’s no need to be snarky online,” Wasden said, cautioning girls.
Wasden said she has no history of a Hockaday student’s decision revoked because of a careless mistake. “It would be silly to miss a great opportunity because of a bad judgment in a moment,” she said. “Be appropriate; choose to chronicle your lives in a way you’d be proud to show your parents.”
An Existential Question
So does privacy exist in the digital world at Hockaday?
The primary uses for tracking software are for instructional purposes, asset recovery and troubleshooting purposes.
Curtis said the measures implemented are to protect students, faculty and staff. But anything someone puts on the school’s network is “about as private as a postcard,” he said, advising students to be intentional about what they plant on the network.
Because the school does not have access to anything a student does outside of school, her digital privacy extends as far as her home network, although, Curtis said, “not even. Someone has access to everything you put up. Anywhere you go, whether on a school or work network, administrators can see what you do.” Even administrators on third party networks could access people’s emails to social media accounts.
Kim McBride, mother to junior Ryan and seventh-grader Maddie, knows that administrators can gain access to her daughters’ accounts but feels comfortable with that. “The only reason they would access [them] is if they had a reason to do that,” she said. “I put trust in the school that they would only access what they absolutely needed to. I have a lot of confidence in this school.”
McBride is on par with the Technology Department’s philosophy. While Curtis has access to every individual’s account on the Hockaday network, he said he does not have the time to investigate everyone on the network, nor is he interested. He compared himself to Mr. Ashton, who could access a student’s locker anytime but chooses not to. “I have professional policies, and also I don’t have the time,” Curtis said.
Curtis would only access an account if a concern was brought to him. “We will never pull up someone’s screen unless they ask,” he said but noted that teachers might do so through DyKnow or other software.
“We respect your privacy, but you should know we have access,” Curtis said, admitting that digital privacy is a “fluid” concept.
Expectations to behave appropriately on Hockaday’s shared network exist for all students. “Ground zero is grounded in trust,” Matthews said. And it is this foundation of trust that allows administrators to give students privacy.
-Tiffany Le, Editor-in-Chief